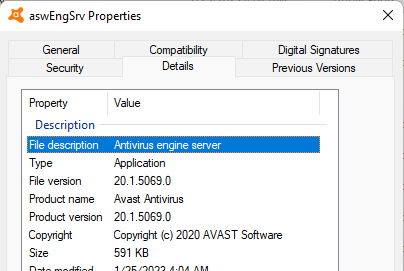
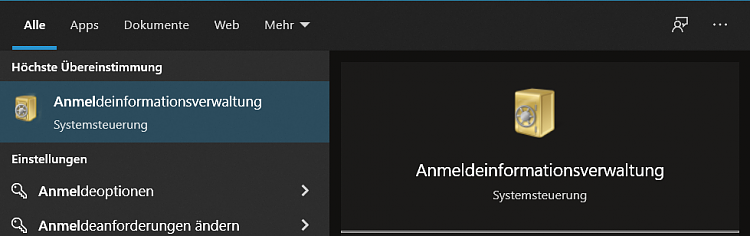
![Avast Threat Labs on Twitter: "Additional detail: The C&C server is derived from a DNS response sent to the specific CNAME (rpc.1qw[.]us). The domain name of CNAME is m.tet.kozow[.]com, and we discovered Avast Threat Labs on Twitter: "Additional detail: The C&C server is derived from a DNS response sent to the specific CNAME (rpc.1qw[.]us). The domain name of CNAME is m.tet.kozow[.]com, and we discovered](https://pbs.twimg.com/card_img/1652378847659130883/7PPB1DXK?format=jpg&name=4096x4096)
Avast Threat Labs on Twitter: "Additional detail: The C&C server is derived from a DNS response sent to the specific CNAME (rpc.1qw[.]us). The domain name of CNAME is m.tet.kozow[.]com, and we discovered
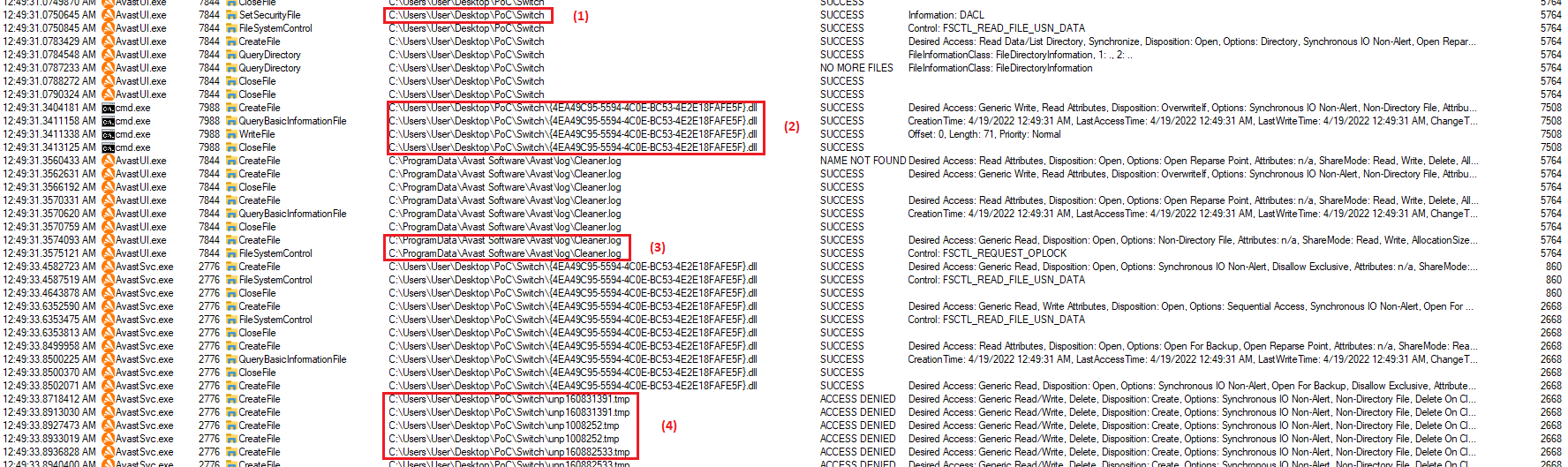
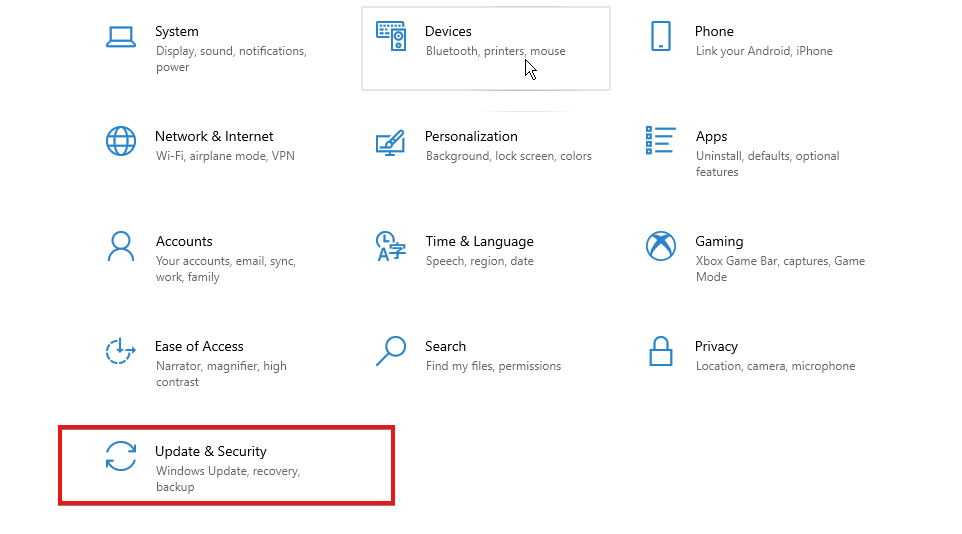
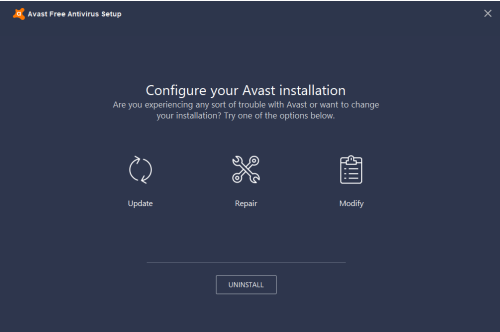
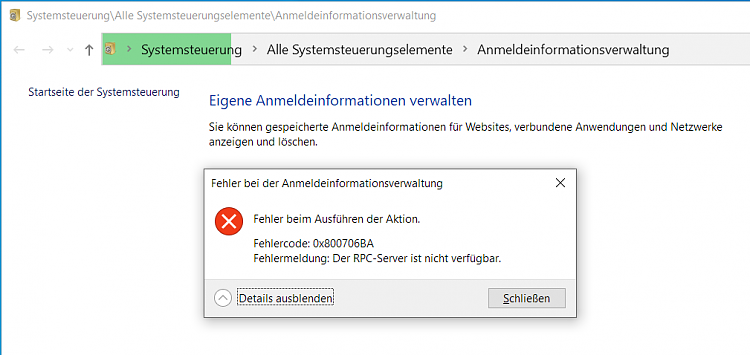
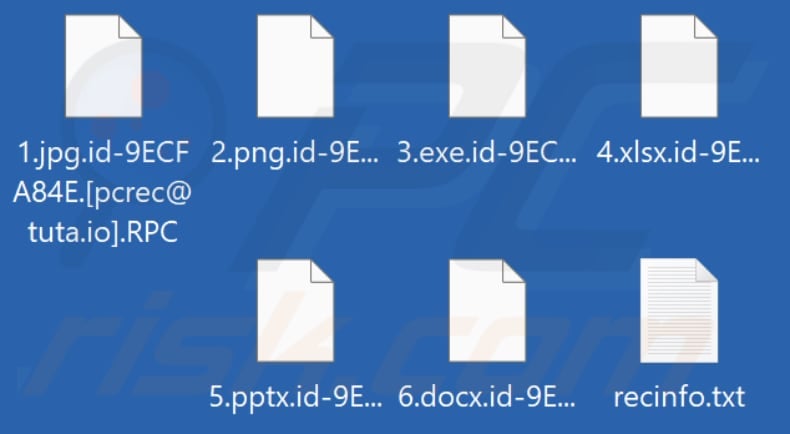
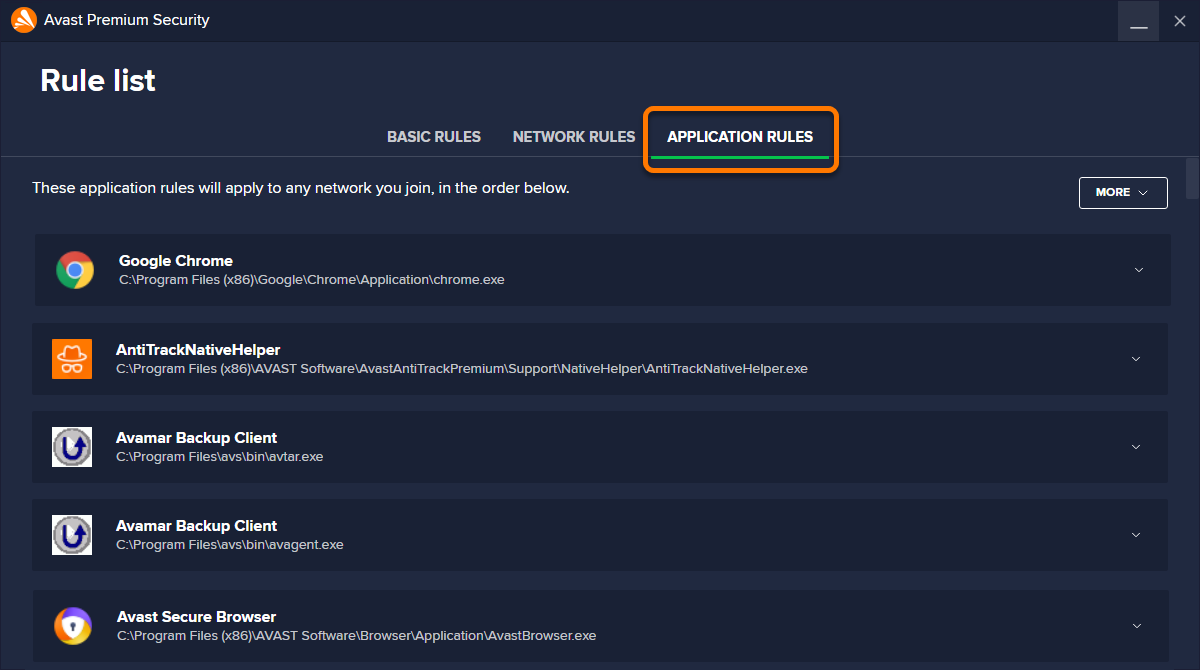
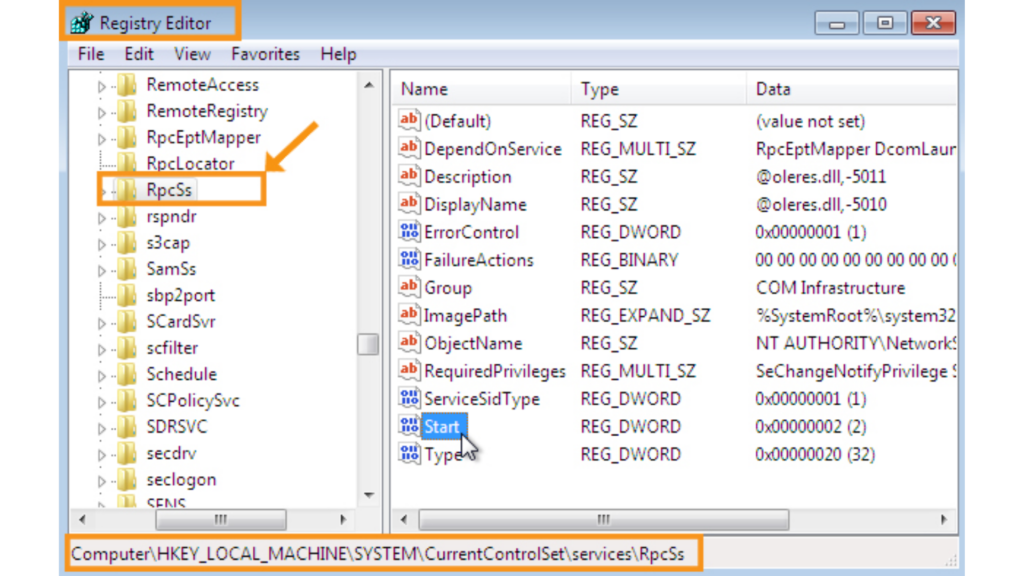
Avast Anti-Virus privileged arbitrary file create on virus quarantine (CVE-2023-1585 and CVE-2023-1587) | the-deniss.github.io